OSS
Introduction of Open Programmable Infrastructure (OPI) Project
Submitted by Roy Schestowitz on Tuesday 21st of June 2022 05:43:50 PM Filed under

-
Linux Foundation launches project to ease smartNIC adoption • The Register
The Linux Foundation wants to make data processing units (DPUs) easier to deploy, with the launch of the Open Programmable Infrastructure (OPI) project this week.
The program has already garnered support from several leading chipmakers, systems builders, and software vendors – Nvidia, Intel, Marvell, F5, Keysight, Dell Tech, and Red Hat to name a few – and promises to build an open ecosystem of common software frameworks that can run on any DPU or smartNIC.
SmartNICs, DPUs, IPUs – whatever you prefer to call them – have been used in cloud and hyperscale datacenters for years now. The devices typically feature onboard networking in a PCIe card form factor and are designed to offload and accelerate I/O-intensive processes and virtualization functions that would otherwise consume valuable host CPU resources.
-
Why Red Hat is joining the Open Programmable Infrastructure Project
As organizations strive for digital transformation, they are in reality seeking to reinvent their business, modernize their processes and push the boundaries of existing IT infrastructure. To address that last point, we frequently see customers exploring alternatives to CPU-centric system architectures, where software running on a central CPU directly controls a set of HW peripherals that offer static functions and/or acceleration capabilities. Supporting this trend is a new class of devices, evolved from SmartNICs but lacking cohesive standards even when it comes to naming - NVIDIA and Marvell call their offerings Data Processing Units (DPU) while Intel refers to their technologies as Intelligent Processing Units (IPUs).
-
Linux Foundation Announces Open Programmable Infrastructure Project to Drive Open Standards for New Class of Cloud Native Infrastructure - Linux Foundation
Data Processing and Infrastructure Processing Units – DPU and IPU – are changing the way enterprises deploy and manage compute resources across their networks; OPI will nurture an ecosystem to enable easy adoption of these innovative technologies
- 6 comments
 Printer-friendly version
Printer-friendly version- Read more
- 2991 reads
 PDF version
PDF version
Events: Patrick Masson, Linux Plumbers Conference, and SUSECON
Submitted by Roy Schestowitz on Tuesday 14th of June 2022 10:28:59 PM Filed under



-
Higher Ed needs to step up to stay relevant as Open Source floods the IT world [Ed: So this is where Patrick Masson moved to after he quit OSI; Danese Cooper Cooper, who worked for famous criminal Bill Gates, is there too]
Grant money is pouring in to support institutions of higher education that are taking a strong position in the adoption of Open Source technologies. 82% of enterprise IT leaders are choosing to work with Open Source vendors, and higher education is stepping up and following suit. In order to stay competitive, campuses must take a critical look at how they manage IT portfolios and seriously consider a larger commitment to their own Open Source strategy.
-
Registration Currently Sold Out, We’re Trying to Add More Places – Linux Plumbers Conference 2022
Back in 2021 when we were planning this conference, everyone warned us that we’d still be doing social distancing and that in-person conferences were likely not to be as popular as they had been, so we lowered our headcount to fit within a socially distanced venue. Unfortunately the enthusiasm of the plumbers community didn’t follow this conventional wisdom so the available registrations sold out within days of being released. We’re now investigating how we might expand the venue capacity to accommodate some of the demand for in-person registration, so stay tuned for what we find out.
-
SUSECON 2022 highlights include container management, edge [Ed: SUSE is selling complexity instead of GNU/Linux. It's also a proprietary software reseller.]
SUSE's annual global conference, SUSECON, held virtually in June, was jam-packed with initiatives and information essential for the future of SUSE and for the open source market.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3139 reads
 PDF version
PDF version
Building the metaverse with open source
Submitted by Rianne Schestowitz on Tuesday 14th of June 2022 09:17:03 AM Filed under
As with all emerging technologies, it's critical to consider the use case and impact to the humans who use it. Immersive virtual and augmented reality devices have unprecedented capabilities to capture, process, store, and utilize data about an individual, including their physical movement patterns, cognitive state, and attention. Additionally, virtual worlds themselves significantly amplify the benefits and problems of today's social media, and require careful implementation of trust and safety systems, moderation techniques, and appropriate access permissions to ensure that users have a positive experience when they venture into these spaces.
As the web evolves and encompasses immersive content and spatial computing devices, it's important to think critically and carefully about the experiences being created, and interoperability across different applications. Ensuring that these virtual worlds are open, accessible, and safe to all is paramount. The prospect of the metaverse is an exciting one, and one that can only be realized through collaborative open source software movements.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2353 reads
 PDF version
PDF version
New versions of Collabora, LibreOffice, KDE Gear released
Submitted by Roy Schestowitz on Monday 13th of June 2022 04:50:21 PM Filed under



Fresh versions of three of the bigger open-source application suites just landed for those seeking to break free from proprietary office apps.
LibreOffice is the highest profile of them, and the project recently put out version 7.3.4, the latest release in the Community version of the suite.
The Document Foundation maintains two versions of LibreOffice; the other is the Enterprise branch.
Both versions are free. The difference is that the Community version is the faster-moving development branch. It's comparable to a free Linux distro, or a short-term Ubuntu release: there's no commercial support, but you may be able to get assistance from other users – in other words, the Community.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 3071 reads
 PDF version
PDF version
Edit PDFs on Linux with these open source tools
Submitted by Rianne Schestowitz on Thursday 9th of June 2022 09:28:39 AM Filed under


If you're looking for a free and safe alternative to proprietary PDF viewing and editing software, it is not hard to find an open source option, whether for desktop or online use. Just keep in mind that the currently available solutions have their own advantages for different use cases, and there's no single tool that is equally great at all possible tasks.
These five solutions stand out for their functionality or usefulness for niche PDF tasks. For enterprise use and collaboration, I suggest ONLYOFFICE or LibreOffice Draw. PDF Arranger is a simple, lightweight tool for working with pages when you don't need to alter text. Okular offers great viewer features for multiple file types, and Xournal++ is the best choice if you want to sketch and take notes in your PDFs.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2268 reads
 PDF version
PDF version
u-blox XPLR-IOT-1 explorer kit embeds cellular IoT, Wi-Fi, BLE, GNSS, and sensors for IoT evaluation
Submitted by Rianne Schestowitz on Wednesday 8th of June 2022 12:23:09 PM Filed under


u-blox XPLR-IOT-1 explorer kit is an all-in-one IoT evaluation platform with cellular IoT, Wi-Fi, Bluetooth Low Energy, and GNSS, plus some sensors to evaluate various IoT products and enable proofs of concepts such as logistics container trackers, industrial automation, sensor-to-cloud applications, and fleet management solutions.
The device’s main module is the u-blox NORA-B106 with a dual-core Arm Cortex M33 microcontroller and Bluetooth LE 5.2 radio that host the application software and control the other modules, namely the SARA-R510S module for LTE-M and NB-IoT cellular connectivity, NINA-W156 2.4 GHz Wi-Fi module, and the MAX-M10S GNNS module. The XPLR-IOT-1 platform is also equipped with an accelerometer, a gyroscope, a magnetometer, and
temperature, humidity, pressure, and ambient light sensors.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2451 reads
 PDF version
PDF version
Rufus for Linux? Here Are the Best Live USB Creating Tools
Submitted by Rianne Schestowitz on Wednesday 8th of June 2022 12:18:21 PM Filed under

Rufus is an open-source utility to create bootable USB drives. It is straightforward to use, with available options to tweak as per your requirements. Not just the ease of use, it is also incredibly fast to make bootable USB drives.
Unfortunately, Rufus is not available for Linux, it is only exclusive to Windows. So, most of us who have used it on Windows, look for Rufus alternatives on Linux.
If you are in the same boat, fret not, we have some excellent alternatives for various use-cases.
Let us explore some Rufus alternatives for Linux...
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2408 reads
 PDF version
PDF version
Conformant open source support for Mali-G57
Submitted by Rianne Schestowitz on Monday 6th of June 2022 04:52:47 PM Filed under

The open source Panfrost driver for Mali GPUs now supports the new Valhall architecture with fully-conformant OpenGL ES 3.1 on Mali-G57, a Valhall GPU. The final Mesa patches are landing today, and the required kernel patches are queued for merge upstream.
Mali-G57 features in new MediaTek Chromebooks with the MT8192 and MT8195 system-on-chips. Collaborans AngeloGioacchino Del Regno and Nícolas F. R. A. Prado are spearheading the mainlining effort for these devices. With Mesa 22.2 and an appropriate kernel, accelerated graphics will work out of the box on Linux on these laptops.
- 2 comments
 Printer-friendly version
Printer-friendly version- Read more
- 2673 reads
 PDF version
PDF version
Top 15 Best Torrent Clients for Linux System in 2022
Submitted by Rianne Schestowitz on Monday 6th of June 2022 12:50:05 PM Filed under

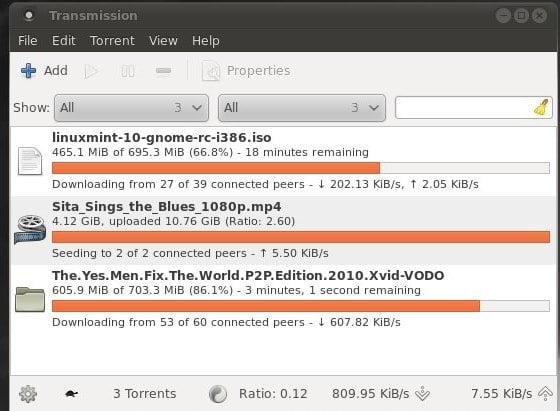
People who need to download bulk files often look for the best torrent client for Linux. Basically, torrents are an excellent source for downloading large documents like motion pictures, Movies, Games, and TV appearances. They transform your PC into part of a host where information is shared as it’s downloaded, so while you’re downloading something from other individuals, you’re likewise helping other people download the bits you’ve just got.
The outcome is an extremely reliable and frequently quick approach to getting your hands on galactic documents. Here come the questions about the best open source torrent client for Linux, which helps get the job done. This article will only discuss open source torrent clients for Linux, leaving some favorite closed source Torrent clients untouched.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2265 reads
 PDF version
PDF version
10 Best Open Source Image Processing Libraries in 2022
Submitted by Rianne Schestowitz on Sunday 5th of June 2022 05:47:14 PM Filed under
In Linux, there are so many codecs, extensions, and libraries for processing images, audio files, and video files. Earlier, we have seen how to play videos smoothly on Linux with all media player codecs. When it comes to talking about the graphics and image section on Linux, you need to find out the suitable extensions or library tools for better performance. Suppose you’re a media enthusiast or you work in a sector where you need to process images in various ways. In that case, you can’t rely upon just the default image process libraries on Linux.
- Login or register to post comments
 Printer-friendly version
Printer-friendly version- Read more
- 2477 reads
 PDF version
PDF version
More in Tux Machines
- Highlights
- Front Page
- Latest Headlines
- Archive
- Recent comments
- All-Time Popular Stories
- Hot Topics
- New Members
digiKam 7.7.0 is released
After three months of active maintenance and another bug triage, the digiKam team is proud to present version 7.7.0 of its open source digital photo manager. See below the list of most important features coming with this release.
|
Dilution and Misuse of the "Linux" Brand
|
Samsung, Red Hat to Work on Linux Drivers for Future Tech
The metaverse is expected to uproot system design as we know it, and Samsung is one of many hardware vendors re-imagining data center infrastructure in preparation for a parallel 3D world.
Samsung is working on new memory technologies that provide faster bandwidth inside hardware for data to travel between CPUs, storage and other computing resources. The company also announced it was partnering with Red Hat to ensure these technologies have Linux compatibility.
|
today's howtos
|







.svg_.png)
 Content (where original) is available under CC-BY-SA, copyrighted by original author/s.
Content (where original) is available under CC-BY-SA, copyrighted by original author/s.

Recent comments
47 weeks 1 day ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 2 days ago
47 weeks 3 days ago
47 weeks 3 days ago
47 weeks 3 days ago