Watch Desktop Linux Apps (like GIMP) Running on Chrome OS [Video]



Linux fans enthusiastic about Google’s effort to bring desktop Linux apps on Chrome OS owe to themselves to watch the following video.
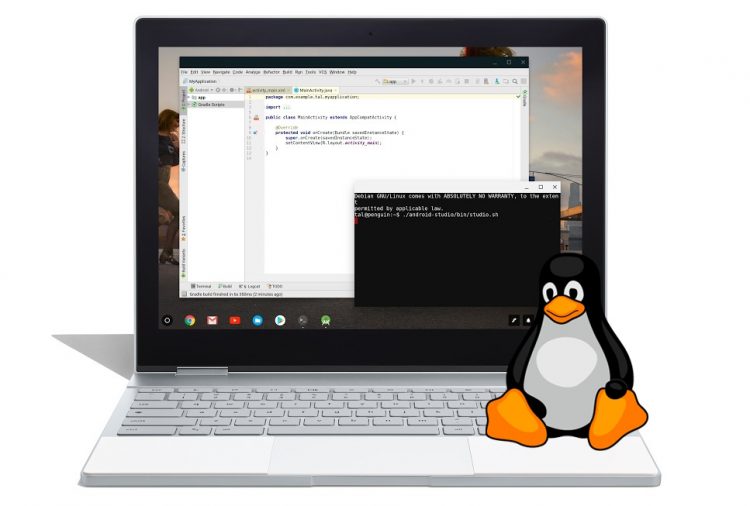
In it, technology YouTuber Lon Seidman demos the current state of the Crostini project (‘Crostini’ is the codename for the “run desktop and CLI Linux apps on Chrome OS” feature we keep gushing about) on both an Intel Chromebox and an ARM-based Chromebook.
This latter demo, of ARM support, is of particular interest.
I had (wrongly, it turns out) assumed Google would restrict Crostini to running on its higher-end Chromebooks, like the pricey Google Pixelbook and the ‘spensive Samsung Chromebook Plus.
-

- Login or register to post comments
 Printer-friendly version
Printer-friendly version- 7346 reads
 PDF version
PDF version
More in Tux Machines
- Highlights
- Front Page
- Latest Headlines
- Archive
- Recent comments
- All-Time Popular Stories
- Hot Topics
- New Members
digiKam 7.7.0 is released
After three months of active maintenance and another bug triage, the digiKam team is proud to present version 7.7.0 of its open source digital photo manager. See below the list of most important features coming with this release.
|
Dilution and Misuse of the "Linux" Brand
|
Samsung, Red Hat to Work on Linux Drivers for Future Tech
The metaverse is expected to uproot system design as we know it, and Samsung is one of many hardware vendors re-imagining data center infrastructure in preparation for a parallel 3D world.
Samsung is working on new memory technologies that provide faster bandwidth inside hardware for data to travel between CPUs, storage and other computing resources. The company also announced it was partnering with Red Hat to ensure these technologies have Linux compatibility.
|
today's howtos
|









.svg_.png)
 Content (where original) is available under CC-BY-SA, copyrighted by original author/s.
Content (where original) is available under CC-BY-SA, copyrighted by original author/s.

More of this
Linux apps on the Acer Chromebook Tab 10